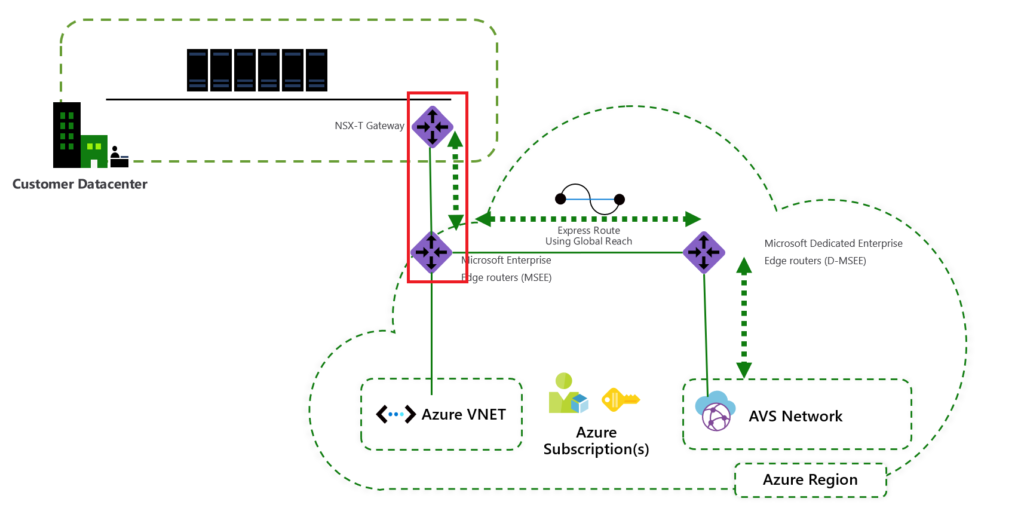
In the previous blogpost we went through Azure VMware Solution(AVS) IPSec VPN setup and to complete hybrid networking between on-prem and AVS we need to configure NSX-T gateway too. As we discussed the target architecture would look like the following diagram.
To start the configuration log in to NSX-T admin GUI and go to Networking tab, under Network Services click on VPN and then choose the Profile tab. Here we are going to create IKE, IPSec and DPD profiles.
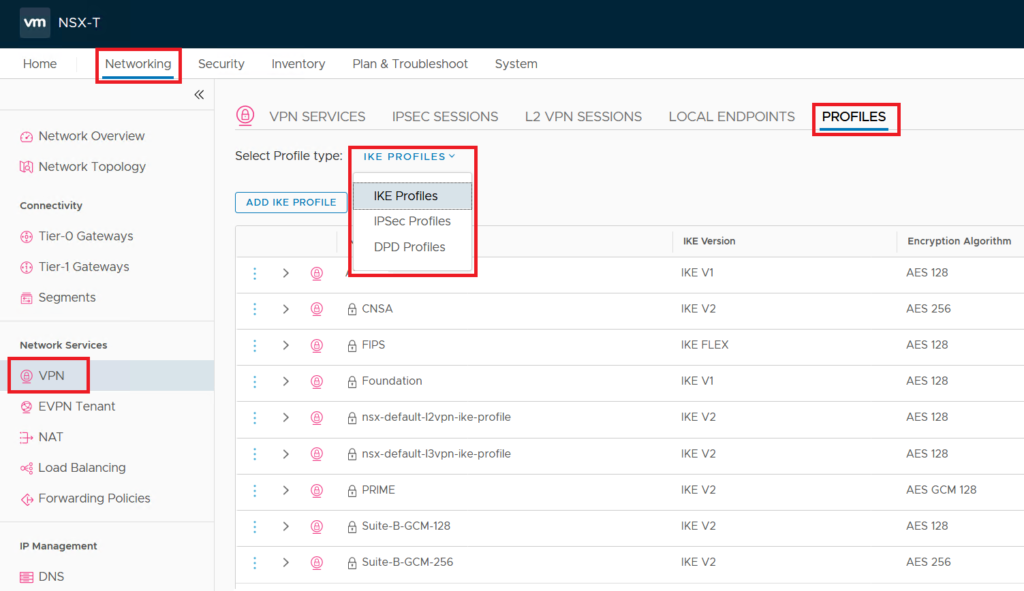
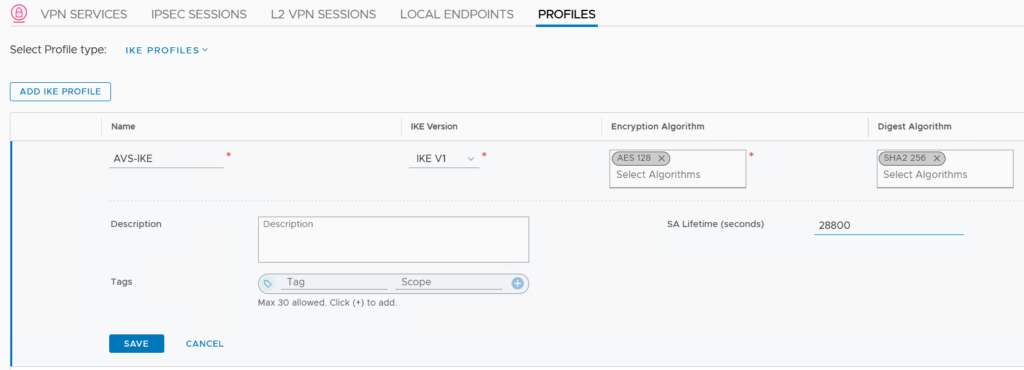
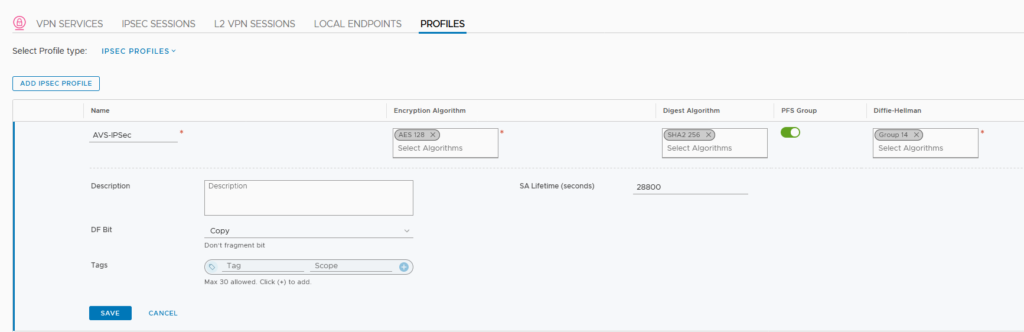
So the configuration here should match what you have configured on Azure’s VPN connection. If you are not sure about that go back to Part 1 of this blog post and check the last step which we configured Pre-shared key and rest of IPSec details. Based on the mentioned configuration ion AVS, the NSX-T profiles has be configured as below.
This is how IKE Profile looks like;
This how IPSec Profile looks like;
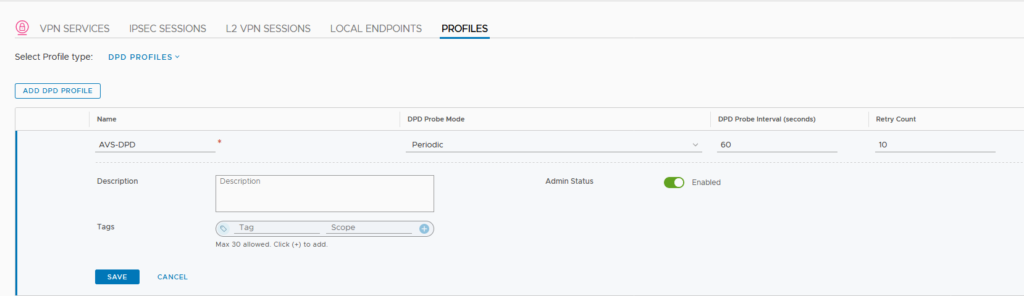
This is how DPD Profile looks like;
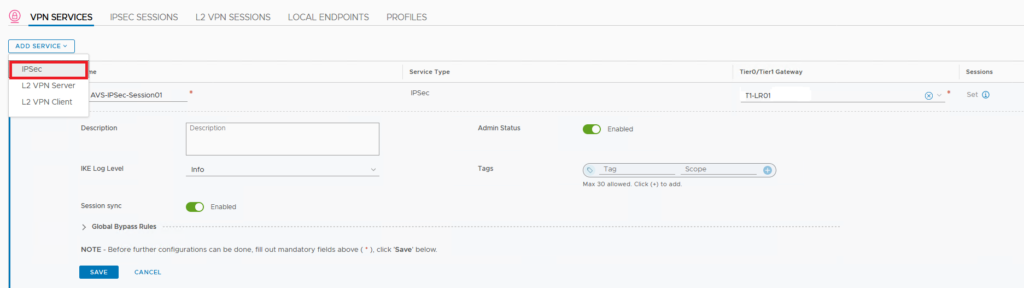
After creating profiles we need to create a VPN Service which define the service and associate it to an T0/T1 Gateway.
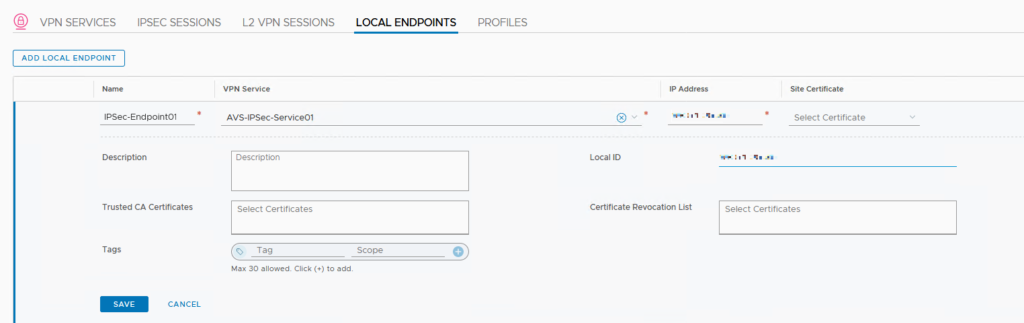
Next we need to create our Local Endpoint. This is the on-prem IPSec tunnel endpoint and if you remember we have sat this public IP address on AVS in the Link IP Address configuration.
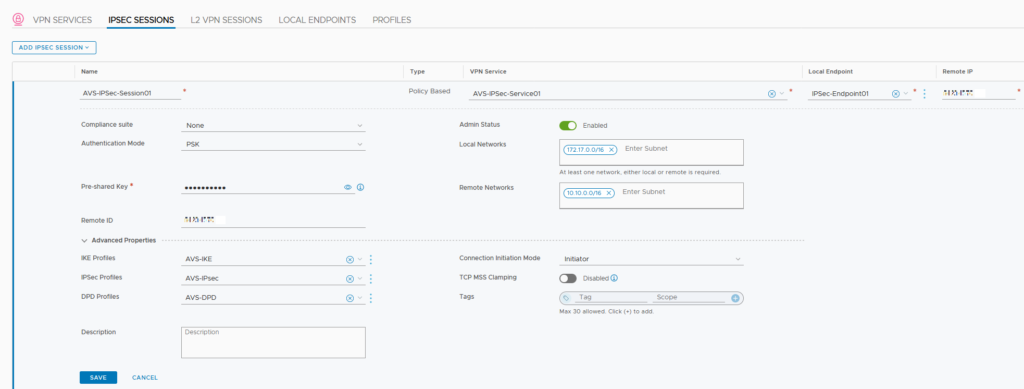
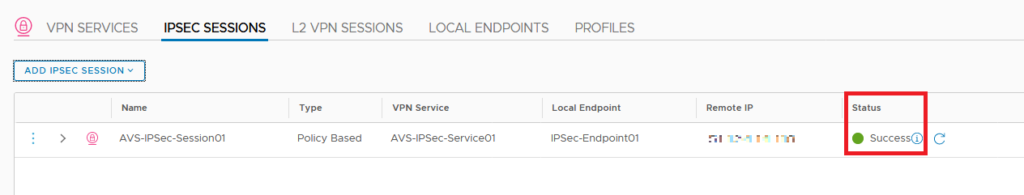
Finally we can get everything together by creating IPSec session. Here we have the option to create either Policy-Based or Route-Based sessions. If you are planning to use BGP for the dynamic routing go ahead an create Route-bsed or if you have a simple setup choose Policy-based. On the step we associate all the profiles we created to VPN Service, Local endpoint and ofcourse our Pre-Shared key. You also need to retrieve the Public IP address on vWAN Hub Gateway and configure it here. In case of Policy-based, you also need to configure CIDR ranges of your local(on-prem) and remote(AVS) networks.
Finally we can check the tunnel status from the same page. You can check the Status column and if it is success then you have the hybrid networking set up that we aimed for.
In the next blogpost we will discuss NSX-T implementation on AVS.